There’s something easy to overlook about EDI. It works quietly—almost invisibly—moving purchase orders, invoices, and payment data between systems without much fanfare. And because it usually just works, it rarely gets the attention it probably deserves.
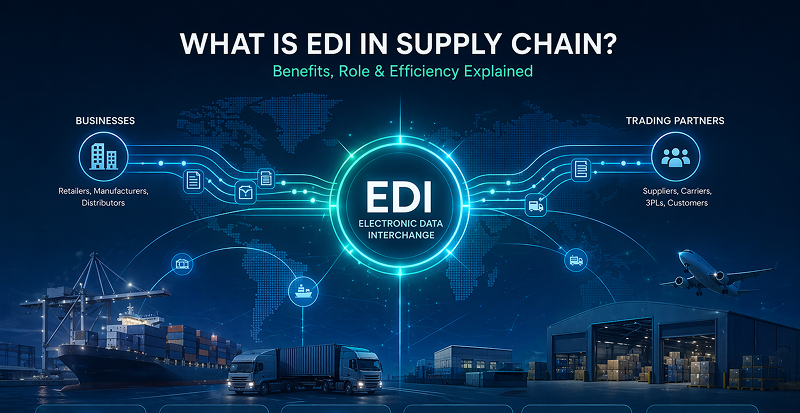
Electronic Data Interchange (EDI), at its core, is the digital infrastructure that allows businesses to exchange critical documents in a structured, automated way. No paper, no manual entry, no delays. It’s efficient, reliable, and—frankly—essential to modern operations. But that same efficiency can create a false sense of security.
Meanwhile, the landscape around it has changed. Cyber threats have become more sophisticated. Regulatory requirements continue to tighten. And data breaches—once occasional—are now, unfortunately, part of the everyday business conversation. It doesn’t take much imagination to see the risk: sensitive financial data moving across systems, often without the level of protection it actually requires.
The real challenge? Many organizations depend heavily on EDI but underestimate the security implications. That gap can lead to serious consequences—financial losses, compliance violations, even strained relationships with trading partners.
So, this isn’t just a technical discussion. It’s a business one. In the sections that follow, we’ll unpack the key security, privacy, and legal risks in EDI—and more importantly, explore practical ways to address them before they become costly problems.
What Is EDI Security?
So what is EDI security, really? It’s one of those terms that gets tossed around in meetings—usually by IT—but rarely unpacked in plain language.
At a basic level, EDI security is the set of safeguards that protect electronic business documents as they move between systems, partners, and networks. Sounds straightforward. It isn’t always.
Several moving parts sit underneath that umbrella. Data encryption, for one, ensures that sensitive information—pricing, bank details, customer data—can’t be read if intercepted. Then there’s authentication, which verifies that the sender and receiver are exactly who they claim to be (no imposters slipping through the cracks). Secure transmission protocols like AS2 or SFTP add another layer, creating controlled channels for data exchange rather than leaving things exposed. And access controls—often overlooked—determine who inside your organization can actually view or modify that data.
Now, here’s where things get interesting. Basic EDI setups may handle document exchange just fine, but “working” doesn’t equal “secure.” Not even close. Secure EDI, on the other hand, builds protection into every step—before, during, and after transmission.
And that’s the shift companies need to make. Because EDI security isn’t just an IT checkbox—it’s risk management. Business-level risk.
Common Security Issues in EDI
Here’s where things tend to get messy.
When people talk about security issues in EDI, they often picture some dramatic cyberattack—hooded hacker, blinking screens, the whole cliché. In reality, the risks are usually quieter. Subtle. And honestly, a bit more dangerous because they go unnoticed.
Start with data breaches during transmission. If EDI documents aren’t properly encrypted, they can be intercepted mid-transfer—like sending sensitive financial data on a postcard instead of in a sealed envelope. It doesn’t happen every day, but when it does, the fallout isn’t small.
Then there’s unauthorized access. Internally or externally. Without tight controls, the wrong person can view—or worse, alter—documents like invoices or payment files. That’s not just inconvenient; it opens the door to fraud.
Another big one? Lack of visibility. Many systems don’t provide real-time insight into transactions, so when something goes wrong, companies are left guessing. What changed? Who touched it? When did it happen? No clear answers.
And let’s not ignore weak authentication processes. Shared logins, outdated credentials—it still happens more often than most teams would admit. Add legacy systems into the mix—platforms built years (or decades) ago without modern security standards—and you’ve got a fragile setup.
Here’s the underlying issue: a lot of EDI environments still rely on outdated or semi-manual processes. They “work,” sure—but they weren’t designed for today’s threat landscape.
The impact? It adds up. Data mismatches, fraudulent transactions, compliance failures—and slower operations because teams are constantly double-checking things that should be automated.
Picture this: an invoice gets intercepted or altered during transmission. A small change—bank account details, maybe. Payment goes out. Nobody notices until it’s too late. That’s not a hypothetical. It happens.
And when it does, it’s rarely just a technical problem. It becomes a business one. Fast.
EDI Legal, Security, and Privacy Issues
This is where EDI stops being just a technical conversation and starts brushing up against legal territory—which, if we’re being honest, is where things get uncomfortable for a lot of organizations.
The EDI legal, security, and privacy issues aren’t theoretical. They’re tied directly to regulations that carry real consequences. Depending on the industry, that might mean HIPAA for healthcare data, GDPR for companies dealing with EU customers, or SOX for financial reporting. Each comes with its own rules about how data is handled, stored, and protected—and EDI sits right in the middle of all that activity.
Then there’s the privacy angle. EDI documents often contain sensitive information—customer details, pricing agreements, bank data. If that information is exposed, even unintentionally, it’s not just a systems failure. It’s a breach of trust. And those are hard to repair.
Audit and record-keeping requirements add another layer. Businesses need to know what happened, when, and who was involved. Not in a vague sense—precisely. Yet many EDI environments still lack clear audit trails or real-time visibility, which makes compliance… tricky, at best.
And liability? That’s the part nobody wants to think about. If a breach occurs, responsibility doesn’t disappear into the system—it lands squarely on the business.
The core issue is this: many organizations don’t have the level of traceability or accountability they actually need. And without it, they’re exposed—to fines, legal challenges, and reputational damage that tends to linger longer than expected.
Because at the end of the day, EDI isn’t just about moving data from point A to point B. It has to prove that the data was handled correctly, securely, and transparently—every single step of the way.
Top EDI Security Risks in Modern Environments
Modern EDI environments aren’t isolated anymore—and that’s both a strength and a weakness.
On one hand, you’ve got ERP systems, warehouse platforms (WMS), CRM tools—all talking to each other, sharing data, keeping operations in sync. On the other hand… those connections aren’t always as seamless as they should be. Small integration gaps creep in. Data doesn’t quite line up. And suddenly, something that should be automated requires manual intervention.
Which brings us to one of the more persistent risks: manual data re-entry. It sounds harmless—just a quick correction here, a workaround there—but every time a human touches the data, the chance of error increases. A mistyped value, a misplaced decimal… it doesn’t take much.
Third-party vulnerabilities are another weak spot. EDI relies heavily on trading partners, vendors, external systems—and if their security posture isn’t solid, yours isn’t either. It’s a shared ecosystem, whether companies like it or not.
And then there’s the lack of real-time monitoring. Many businesses still operate with delayed visibility, meaning issues aren’t caught as they happen—they’re discovered after the fact. Sometimes much later.
The common thread here? Disconnected systems. Not completely broken, just… loosely stitched together.
The impact tends to compound over time: delays in processing, data inconsistencies, compliance gaps that are harder to trace. Individually, these issues might seem manageable. Together, they create a level of risk that’s difficult to ignore—and even harder to control.
EDI Security Best Practices
If you ask five different IT teams about EDI security best practices, you’ll probably get five slightly different answers. But the fundamentals? They don’t really change—just the level of discipline in applying them.
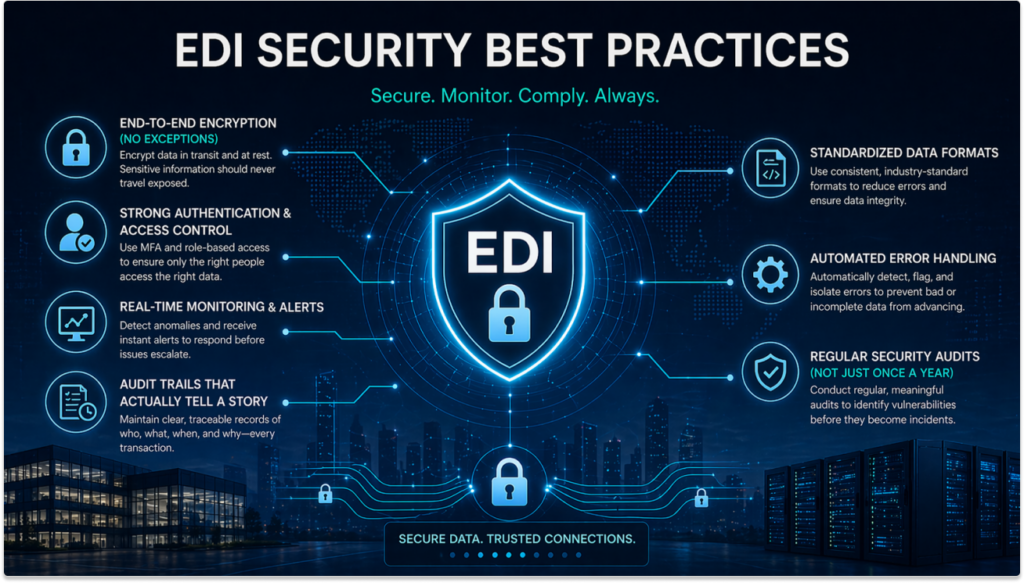
End-to-End Encryption (No Exceptions)
Start here. Always here.
Data needs to be encrypted while it’s moving and while it’s sitting still. Too many setups protect one and ignore the other—which, frankly, defeats the point. Sensitive data—pricing, payment info, customer records—should never travel exposed. Not even briefly.
Strong Authentication & Access Control
Passwords alone don’t cut it anymore. They just don’t.
Multi-factor authentication (MFA) adds that extra layer, making unauthorized access far less likely. Pair that with role-based access controls—so only the right people see the right data—and you’ve already closed off a big chunk of risk.
Real-Time Monitoring & Alerts
Problems rarely announce themselves politely.
You need systems that catch anomalies as they happen—unusual transaction patterns, failed transfers, unexpected changes. Waiting for a weekly report? That’s too late. Real-time alerts give you a chance to respond before things spiral.
Audit Trails That Actually Tell a Story
Every transaction should leave breadcrumbs.
Who sent it, who received it, what changed, when it happened—clear, traceable records. Not vague logs buried somewhere. This is critical for compliance, yes, but also for basic accountability when something goes wrong.
Standardized Data Formats
This one sounds… less exciting, but it matters.
When data formats vary between systems, inconsistencies creep in. Mapping errors. Misinterpretations. Standardization reduces that friction and keeps transactions clean from the start.
Automated Error Handling
Here’s where automation earns its keep.
Instead of letting bad or incomplete data slip through, systems should flag and isolate issues automatically. No manual chasing. Or at least, much less of it.
Regular Security Audits (Not Just Once a Year)
Security isn’t static. Neither are threats.
Regular audits—real ones, not checkbox exercises—help identify weak spots early. Before they become incidents.
How Automation Solves EDI Security Challenges
Here’s the thing—most EDI security problems don’t start as “security” problems. They start as process problems. Manual workarounds. Disconnected systems. Gaps that people quietly patch over just to keep things moving.
And that’s exactly where automation changes the equation.
When EDI processes are automated end-to-end, a lot of those risks simply… disappear. Not magically, but structurally. Data doesn’t need to be re-entered, so human error drops off. Transactions move in real time, which means fewer delays—and fewer opportunities for something to go unnoticed. Even compliance becomes easier to manage because everything is tracked automatically.
This is where platforms like EZConnect come into play.
Instead of relying on fragmented systems, EZConnect creates a unified, real-time data flow between ERP, WMS, CRM, and trading partners. No batch delays. No manual re-keying. Just direct integration. It also validates transactions as they happen—flagging incomplete or suspicious data before it causes downstream issues. That alone can prevent a surprising number of problems.
And then there’s visibility. Full audit trails. Real-time monitoring. Clear transaction tracking across partners. You’re not guessing anymore—you actually know what’s happening.
The result? Fewer errors. Faster processing. Stronger compliance posture.
Or, put more simply—less firefighting, more control.
Because at a certain point, improving EDI security isn’t about adding more layers on top of broken processes. It’s about fixing the process itself.
The Future of EDI Security
If you zoom out a bit, the direction EDI security is heading feels… inevitable.
AI is already stepping in—not in some futuristic, sci-fi way—but quietly, behind the scenes. Monitoring transactions, spotting anomalies, flagging risks before a human would even notice. It’s faster. Less forgiving, too. In a good way.
At the same time, real-time compliance validation is becoming the expectation, not the exception. Businesses won’t just hope they’re compliant—they’ll know, instantly.
There’s also a noticeable shift toward zero-trust security models. Trust nothing. Verify everything. It sounds harsh, but given how interconnected systems have become, it makes sense.
And maybe most importantly, integration platforms are taking center stage. Because in the end, secure EDI isn’t just about locking things down—it’s about connecting everything properly, without the cracks where problems tend to hide.
Conclusion: Turning EDI Security into a Competitive Advantage
At this point, it should be pretty clear—EDI security isn’t just a “nice to have” tucked away in the IT backlog. It’s central. Maybe even mission-critical.
We’ve looked at the risks: data breaches, weak authentication, compliance gaps, those lingering legacy systems that sort of work until they don’t. And the fixes aren’t mysterious either—encryption, access controls, real-time monitoring, audit trails. Layered, practical steps that actually reduce exposure.
But here’s the shift that matters: when you combine those best practices with automation and proper integration, EDI security stops being reactive. It becomes proactive. Strategic, even.
Because secure EDI doesn’t just protect the business—it enables it. Faster transactions. Fewer errors. Stronger, more reliable partner relationships.
And that’s really the takeaway.
Secure EDI isn’t a cost center. It’s leverage.